
How Scammers Are Using AI to Target Travelers
AI is making travel scams increasingly difficult to spot.
Cybersecurity threats, protection strategies, and best practices

AI is making travel scams increasingly difficult to spot.

Smart and compellingly twisty supernatural mysteries, most of them not even in German.

Increase your privacy, remove annoyances, and reset your algorithm.
"Come on, honey, let's go on a little hike..."

Make everyone's favorite X alternative even more welcoming.
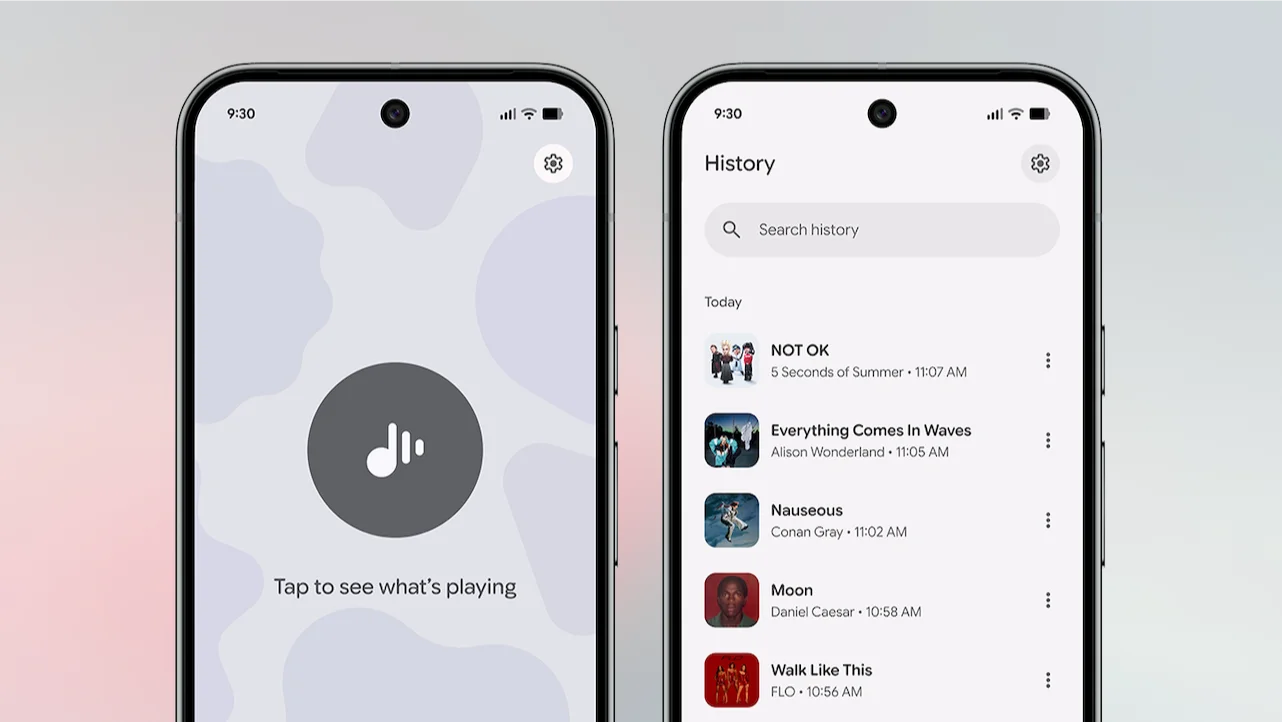
See all the songs you heard while you were hanging out in the hip cafe down the street.
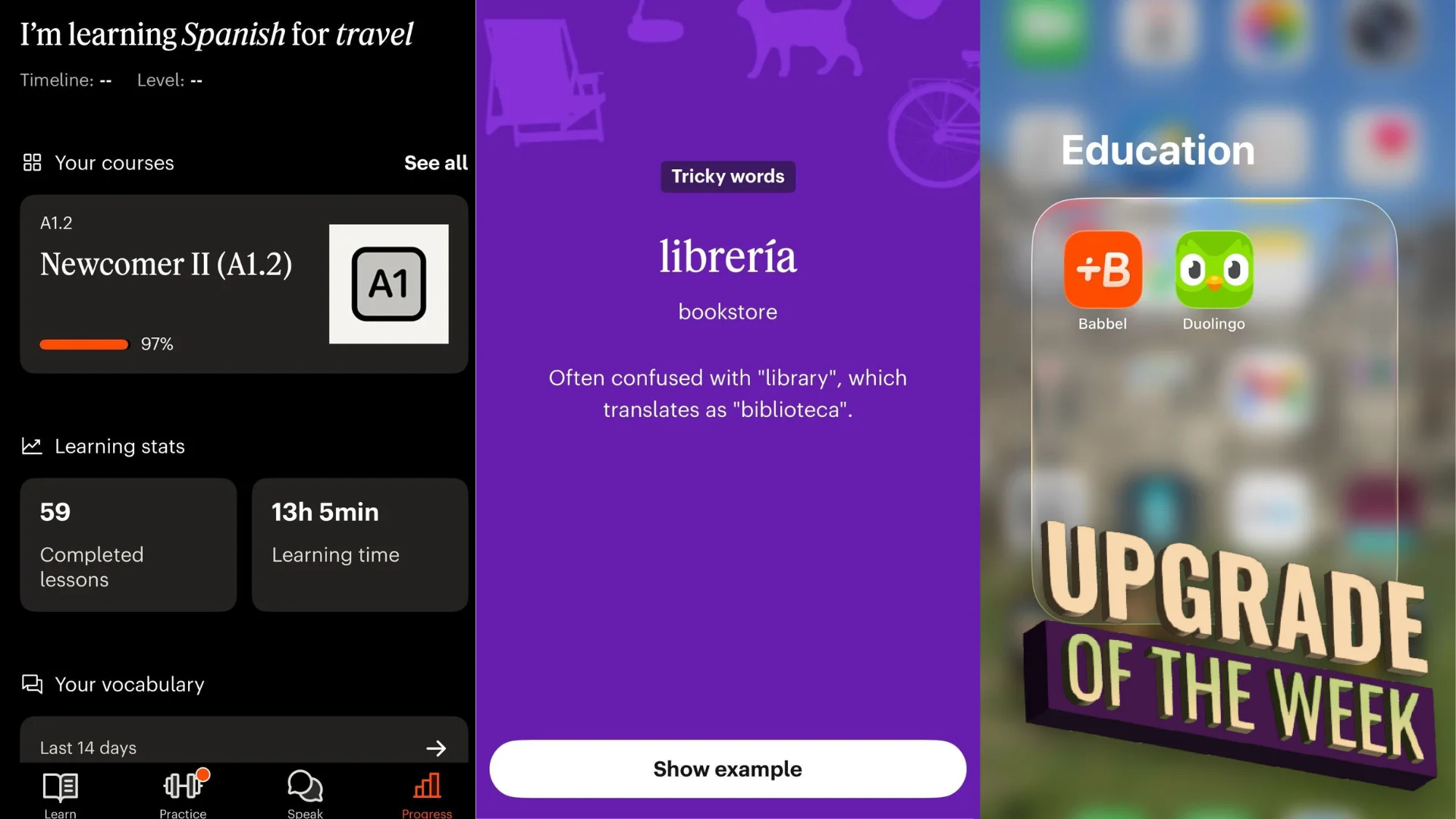
After a 300-day streak that left me unable to construct a sentence, I finally made the switch.

Google packed a bunch of new features and changes into this latest Pixel Drop.

Take control of your vertical video experience.

A bunch of horror movies that suck (but not like that).

Salesforce on Tuesday launched an entirely rebuilt version of Slackbot, the company's workplace assistant, transforming it from a simple notification tool into what executives describe as a fully...
Written by: Ken Huang, CSA Fellow, Co-Chair of CSA AI Safety Working Groups Hammad Atta, Founder & AI Technology Advisor, Qorvexconsulting Research Dr. Yasir Mehmood, AI 5G & IoT Systems ...
Introduction Last month’s disclosure of CVE 2025-55812, known as React2Shell, provided a reminder of how quickly modern threat actors can operationalize newly disclosed vulnerabilities, particu...
Introduction: Why securing AI is now a security priority AI adoption is at the forefront of the digital movement in businesses, outpacing the rate at which IT and security professionals can set...
Agentic workforce is scaling faster than identity and security frameworks can adapt SEATTLE – Feb. 5, 2026 –The latest survey report from the Cloud Security Alliance (CSA), the world’s leading not-for...
Every security team I talk to is having the same conversation right now. Their developers are shipping AI agents — coding assistants, autonomous workflows, LLM-powered tools that can browse the web, e...
Most of us grew up professionally in a world where “secure access” meant encrypt the tunnel and harden what’s exposed. VPNs, TLS/mTLS, WAFs, EDR, patching, detection, response... the whole modern stac...
If your organization is experimenting with AI agents, copilots, or AI services accessed via API, you’ve probably created more identities than you intended. These non-human identities (service accounts...
India’s banking system is undergoing a critical shift in how digital trust is established. With the rise of phishing, impersonation fraud, and look-alike banking websites, the Reserve Bank of India (R...
This is the first blog in a seven-part series on identity security as AI security. TL;DR: AI agents can expand an organization’s attack surface by 100 times, not by doing more but by doing i...