AI Security: When Authorization Outlives Intent
This is the second blog in a seven-part series on identity security as AI security. TL;DR: A silent breach rippled through the SaaS world in August 2025: demanding no ransomware demand, no s...
Cybersecurity threats, protection strategies, and best practices
This is the second blog in a seven-part series on identity security as AI security. TL;DR: A silent breach rippled through the SaaS world in August 2025: demanding no ransomware demand, no s...
Agentic AI is no longer experimental. It’s already operating inside production environments, automating workflows, moving data, calling APIs, and making decisions at machine speed. For organizations i...
Executive Summary This document applies MAESTRO Framework (7-layer Agentic AI Threat Model) to the OpenClaw codebase, identifying specific threats at each layer and detailing mitigation strategies bas...
I've spent my career as an elite security researcher hunting vulnerabilities. My job has always been to think like an attacker: find the gaps and exploit the loopholes. When I bring that same mindset ...
This blog was published on February 19, 2026 with the latest information regarding the release of CCM v4.1. On January 28, CSA released version 4.1 of the Cloud Controls Matrix (CCM), succeeding CCM v...
In the landscape of modern enterprise IT, cloud security posture management (CSPM) often takes center stage by focusing on the underlying multi-cloud infrastructure and detecting misconfigurations. Ho...
Artificial intelligence is reshaping the cyber threat landscape as attackers have already begun weaponizing AI to dramatically accelerate phishing, reconnaissance, payload development, and attack exec...
How AI is blowing cybersecurity apart, taking us back to our beginnings, and reforging our foundations. A star dies slowly. Then all at once. A star lives billions of years in tension. Thermal ...
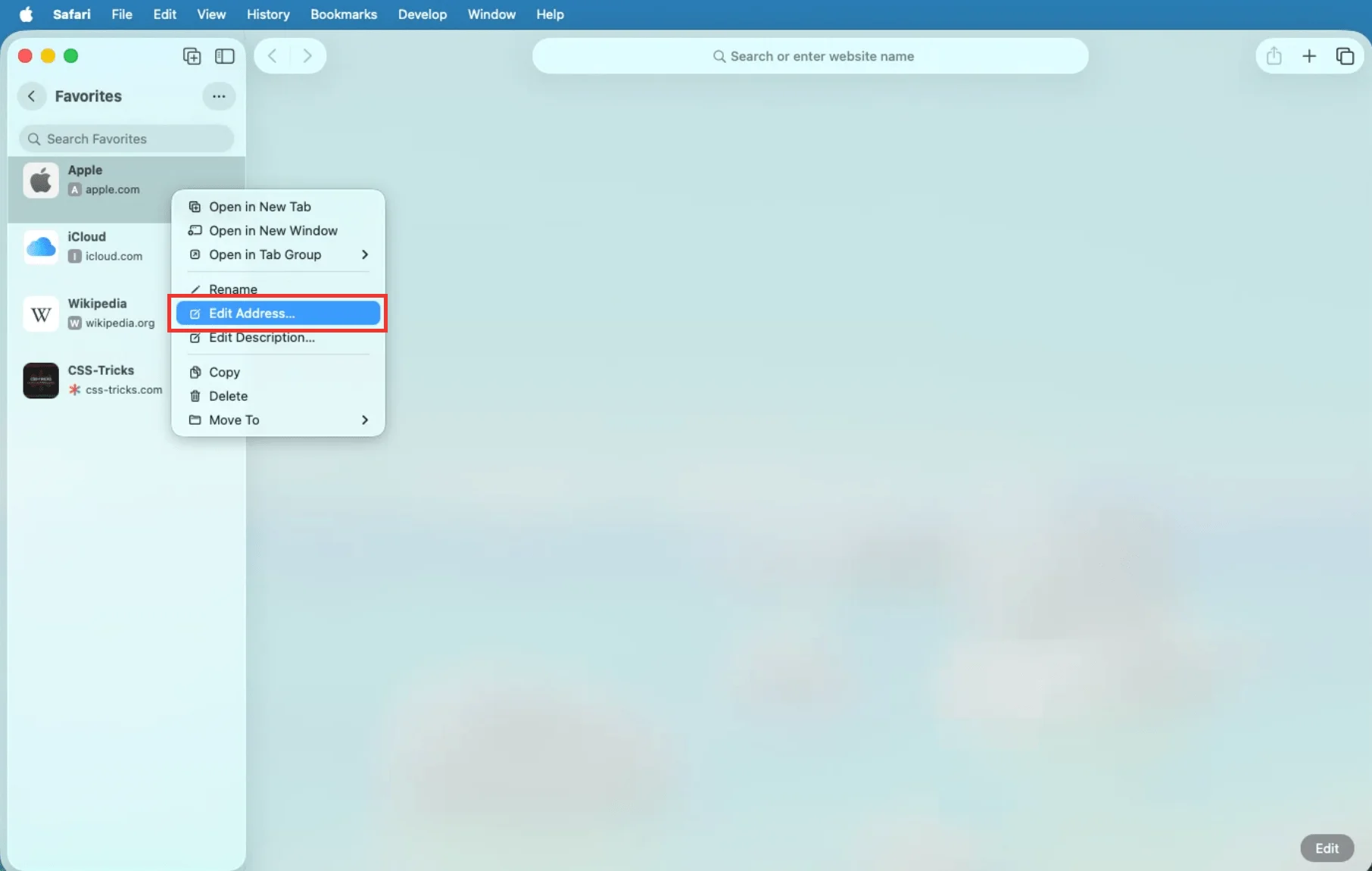
Browsers don't just let you bookmark web pages. You can also bookmark JavaScript, allowing you to do so much more than merely save pages. A Complete Guide to Bookmarklets originally published on CSS-T...
Read an explanation of the recent CVE-2026-2441 vulnerability that was labeled a "CSS exploit" that "allowed a remote attacker to execute arbitrary code inside a sandbox via a crafted HTML page." An E...

From automatic phone locking to Express Pay, the latest Pixel Drop delivers streamlining.

Is it really a bad thing, though? Maybe not.

Calling Cards are finally perfect.

Samsung's hottest phones come with some really nice freebies!
Catch up on the latest Python news: pandas 3.0 breaking changes, Python 3.15 alpha JIT gains, PyTorch 2.10 deprecations, and PSF updates.

Do you have complex logic and unpredictable dependencies that make it hard to write reliable tests? How can you use Python's mock object library to improve your tests? Christopher Trudeau is back on t...